Archive
Backing up smart and static groups from Jamf Pro
When working with smart and static groups on Jamf Pro, especially more complex smart groups, I prefer to download then and back them up to GitHub or a similar internal source control tool. The reasons I do this are the following:
- I have an off-server backup for the groups
- I can track changes to the groups
- If needed, I can make a change to a smart group and upload via the API instead of having to edit in the web console.
Up until recently, I didn’t have a good process for handling this but I was able to develop a way as part of working with an engineer from Jamf. After some work, I was able to build two scripts which do the following:
- Use the Jamf Pro API to identify the Jamf Pro ID numbers of the smart and static groups.
- Download each group as an XML file using its Jamf Pro ID number.
- Format the downloaded XML.
- Identify the display name of the group.
- Identify if it was a smart or static group.
- Save the downloaded XML as Group Name Here.xml to a specified download directory, based on whether it was a smart or static group.
For more details, please see below the jump.
Backing up configuration profiles from Jamf Pro
When working with configuration profiles on Jamf Pro, I prefer to download and back them up to GitHub or a similar internal source control tool. The reasons I do this are the following:
- I have an off-server backup for the profiles
- I can track changes to the profiles
Up until recently, this had been a manual process for me where I would download the profiles in question from the server and then upload them to my source control tool.
My process looked like this:
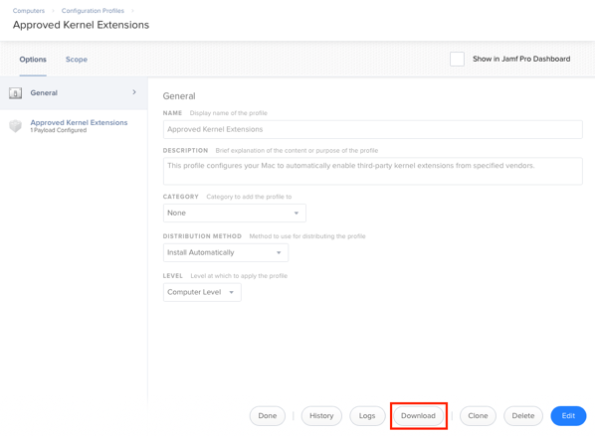
1. Download the profiles from the Jamf Pro server using the Download button.
2. Remove the code-signing and formatting the profile using a process similar to the one described in the link below:
https://macmule.com/2015/11/16/making-downloaded-jss-configuration-profiles-readable/
3. Move the profile to the correct directory in my source control repo.
4. Review changes and commit to the repo.
However, as I’ve started using profiles more, this process got cumbersome and I wanted to automate at least the download part of the process. After some work, I was able to build two scripts which do the following:
- Use the Jamf Pro API to identify the Jamf Pro ID numbers of the configuration profiles.
- Download each profile using its Jamf Pro ID number
- Decode and format the profile
- Identify the display name of the profile
- Save the profile as Display Name Here.mobileconfig to a specified download directory.
For more details, please see below the jump.
Session videos from Jamf Nation User Conference 2018 now available
Jamf has posted the session videos for from Jamf Nation User Conference 2018, including the video for my “Providing the Best Mac Experience Possible, From the Mac CoE Team with ❤️” session.
For those interested, all of the the JNUC 2018 session videos are available on YouTube. For convenience, I’ve linked my session here.
T2, FileVault and brute force attack protection
Apple recently released an overview document for its new T2 chip, which includes how the new T2 chip-equipped Macs have new protections against brute force attacks. This protection only applies if FileVault is enabled and is similar in concept to how iOS devices set with passcodes are protected against brute force attacks.
On iOS, if an incorrect passcode is entered more than five times, a one minute delay is set.

After the sixth try, the delay is now five minutes and the delays get longer from there until the device has the 10th wrong passcode entered and the device wipes.

On Apple iOS devices with a Secure Enclave, those delays are enforced by the Secure Enclave processor. Similarly, the T2 chip-equipped Macs also have a Secure Enclave processor which is managing access attempts and introducing delays.
For Macs with Secure Enclave, the enforcement looks like this:
- 30 unlock attempts via using the password at the login window or target disk mode
- 10 unlock attempts via using the password in Recovery Mode
- 30 unlock attempts for each enabled FileVault recovery mechanism
- iCloud recovery
- FileVault personal recovery key
- FileVault institutional recovery key
The maximum number of unlock attempts is 90, regardless of the mix of methods used. After 90 attempts, the Secure Enclave processor will no longer process any requests to do the following:
- Unlock the volume
- Decrypt the volume
- Verify the password / recovery key
Delays are also imposed on macOS between attempts.

So what happens after 90 attempts? Does the Mac lock forever and become a paperweight?
After checking with AppleCare Enterprise, the answer is that the Mac will not be a paperweight, but that the Mac’s boot drive will need to be erased before it can be used again. This approach helps make sure that the Mac is still usable, but also ensures that the encrypted data stored on the boot drive is no longer recoverable.
For more information about brute force protection for encrypted iOS and macOS devices, I recommend checking out Apple’s currently available white papers:
Recent Comments