Archive
Security Update 2017-001 being pushed to both macOS 10.13.0 and 10.13.1
To fix the vulnerability popularly referred to as #IAMROOT , Apple has begun pushing Security Update 2017-001 to Macs running the following OS versions:
- macOS 10.13.0
- macOS 10.13.1
This update is being deployed using the same automated installation mechanism that Apple previously used to deploy OS X NTP Security Update 1.0 back in 2014, where Security Update 2017-001 is being silently downloaded and installed on vulnerable Macs.

For more details, please see below the jump.
Blocking logins to the root account on macOS High Sierra
A security vulnerability was discovered in macOS High Sierra today, where you could enable and log into the root account without providing a password.
Update 11-29-2017: Apple has released Security Update 2017-001 to fix this issue. Please install this update as soon as possible.
Update 11-30-2017: Apple is now automatically installing Security Update 2017-001 on vulnerable Macs.
To address this this issue until Apple releases an update to fix it, there’s two steps you can take which will block logins to the root account:
- Set a password for the root account on your Mac
- Change the root’s account’s login shell to /usr/bin/false
When you set the root account’s login shell to /usr/bin/false, the shell is changed to point to a command that does nothing except return a status code which reports an error. The login process will interpret that error status code as being a failed login, so it will stop the login process at that point and prompt for the password again.
Since the login process will always receive the error code from the false command, the login process will never succeed. For more details, see below the jump.
First Boot Package Install Generator.app now adds product identifier tags to its packages
As a follow-up to Greg Neagle’s discovery that product identifiers are now needed to ensure best results when adding additional packages to macOS High Sierra OS installers, I’ve updated First Boot Package Installer Generator.app to add product identifiers by default to the firstboot packages created by this tool.
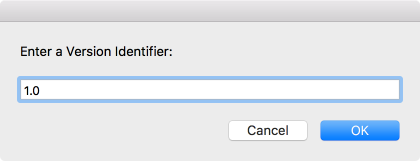
The product identifier values will be the user-selected Package Identifier followed by the Version Identifier.

These values will appear in the firstboot package’s distribution file as shown below:

For those who need this capability, an installer for First Boot Package Install Generator.app 1.7 can be downloaded via the link below:
https://github.com/rtrouton/First_Boot_Package_Install_Generator/releases/tag/1.7
Enabling Touch ID authorization for sudo on macOS High Sierra
My colleague @mikeymikey brought this tweet by Cabel Sasser to my attention yesterday:
I have a Touch ID-enabled MacBook Pro and use sudo frequently, so I’ve implemented this on my own laptop. For more details, see below the jump.
APFS encryption status check script
As part of working Apple File System, I’ve developed a script which is designed to check and report the status of encrypted Apple File System (APFS) drives. Currently, here’s what the script is detecting and reporting:
It first checks to see if a Mac is running 10.13.x or higher. If the Mac is question is running 10.13.x or higher, the script reports if it is using encryption on an APFS drive and gives the encryption or decryption status.
If encrypted, the following message is displayed:
FileVault is On.

If not encrypted, the following message is displayed:
FileVault is Off.

If encrypting, the following message is displayed:
Encryption in progress:
How much has been encrypted is also displayed.

If decrypting, the following message is displayed without quotes:
Decryption in progress:
How much has been decrypted is also displayed.

If run on a drive which is not using APFS, the following message is displayed:
Unable to display encryption status for filesystems other than APFS.

The script is available below and here on my GitHub repository:
https://github.com/rtrouton/rtrouton_scripts/tree/master/rtrouton_scripts/check_apfs_encryption
I’ve also built a Jamf Pro Extension Attribute:
This file contains bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters
| #!/bin/bash | |
| osvers_major=$(sw_vers -productVersion | awk -F. '{print $1}') | |
| osvers_minor=$(sw_vers -productVersion | awk -F. '{print $2}') | |
| ERROR=0 | |
| # Checks to see if the OS on the Mac is 10.x.x. If it is not, the | |
| # following message is displayed without quotes: | |
| # | |
| # "Unknown Version Of macOS" | |
| if [[ ${osvers_major} -ne 10 ]]; then | |
| echo "Unknown Version Of macOS" | |
| fi | |
| # Checks to see if the OS on the Mac is 10.13 or higher. | |
| # If it is not, the following message is displayed without quotes: | |
| # | |
| # "APFS Encryption Not Available For This Version Of macOS" | |
| if [[ ${osvers_major} -eq 10 ]] && [[ ${osvers_minor} -lt 13 ]]; then | |
| echo "APFS Encryption Not Available For This Version Of macOS" | |
| fi | |
| if [[ ${osvers_major} -eq 10 ]] && [[ ${osvers_minor} -ge 13 ]]; then | |
| # If the OS on the Mac is 10.13 or higher, check to see if the | |
| # boot drive is formatted with APFS or HFS+ | |
| boot_filesystem_check=$(/usr/sbin/diskutil info / | awk '/Type \(Bundle\)/ {print $3}') | |
| # If the drive is formatted with APFS, the fdesetup tool will | |
| # be available and is able to display the encryption status. | |
| if [[ "$boot_filesystem_check" = "apfs" ]]; then | |
| # If encrypted, the following message is | |
| # displayed without quotes: | |
| # "FileVault is On." | |
| # | |
| # If encrypting, the following message is | |
| # displayed without quotes: | |
| # "Encryption in progress:" | |
| # How much has been encrypted of of the total | |
| # amount of space is also displayed. | |
| # | |
| # If decrypting, the following message is | |
| # displayed without quotes: | |
| # "Decryption in progress:" | |
| # How much has been decrypted of of the total | |
| # amount of space is also displayed | |
| # | |
| # If not encrypted, the following message is | |
| # displayed without quotes: | |
| # "FileVault is Off." | |
| ENCRYPTSTATUS=$(fdesetup status | xargs) | |
| if [[ -z $(echo "$ENCRYPTSTATUS" | awk '/Encryption | Decryption/') ]]; then | |
| ENCRYPTSTATUS=$(fdesetup status | head -1) | |
| echo "$ENCRYPTSTATUS" | |
| else | |
| ENCRYPTSTATUS=$(fdesetup status | tail -1) | |
| echo "$ENCRYPTSTATUS" | |
| fi | |
| else | |
| echo "Unable to display encryption status for filesystems other than APFS." | |
| fi | |
| fi | |
| exit $ERROR |
Downloading macOS Sierra from the Mac App Store
Now that macOS High Sierra has been released, it’s become more difficult to access the macOS Sierra installer in the Mac App Store (MAS) for those who still need it.
Previous versions of OS X and Mac OS X which were purchased by an Apple ID will appear in the MAS’s Purchased list for that Apple ID, but macOS Sierra is an exception because it did not need to be purchased using an Apple ID.

Fortunately, Sierra has not been removed from the MAS and it is still available for download. Apple has a KBase article, available via the link below, which shows how to access the macOS Sierra page in the Mac App Store:
https://support.apple.com/HT208202
To access the macOS Sierra page directly, please click on the link below:
https://itunes.apple.com/us/app/macos-sierra/id1127487414?ls=1&mt=12
That link should open the MAS and take you to the macOS Sierra download page.

In the event that you’re blocked from downloading macOS Sierra, you should be able to download it in a virtual machine. I have a post on how to do this, available via the link below:
Session videos from Jamf Nation User Conference 2017 now available
Jamf has posted the session videos for from JAMF Nation User Conference 2017, including the video for my Apple File System session.
For those interested, all of the JNUC 2017 session videos are available on YouTube. For convenience, I’ve linked my session here.
Adding installer package code-signing to AutoPkg workflows
As part of building an AutoPkg workflow to create installer packages, one of the requirements I was given was that any packages that weren’t already signed by the vendor needed to be signed using a Developer ID Installer signing certificate.

Signing installer package is not usually an outcome of most AutoPkg workflows, since code signature verification can be used at the download end to make sure that the application is what it is supposed to be. However, there were several good reasons for adding a package signing step to the workflow, including:
- It is now necessary to sign packages before you’ll be able to use them as part of NetInstall sets
- The InstallApplication MDM command requires that macOS installer packages be signed with an appropriate certificate
After some research and testing, I was able to incorporate installer package signing into my AutoPkg workflow and am now able to automatically sign installer package as they’re generated by my package creation workflows. For more details, see below the jump.
Implementing log rotation for the Jamf Infrastructure Manager logs on Red Hat Enterprise Linux
A while back, I had set up the Jamf Infrastructure Manager (JIM) in a VM running Red Hat Enterprise Linux (RHEL) to provide a way for a Jamf Pro server hosted outside a company’s network to be able to talk to an otherwise inaccessible Active Directory domain. The JIM software has been running fine since I configured it, but I recently needed to take a look at the JIM logs as part of diagnosing another issue.
For those not familiar with the JIM software, it has several log files and those logs are available in the following location on RHEL:
/var/log/jamf-im-launcher.log
/var/log/jamf-im.log
/var/log/jamf-im-pre-enroll.log

When I checked the logs, I noticed that /var/log/jamf-im.log had grown to almost 500 MBs in size.
Considering this log is a plaintext file, that’s a big log file and it seemingly had been not been rotated or otherwise changed since I first installed the JIM software. To help make sure that the host VM would not eventually run out of space because of this growing log file, I needed to implement log rotation for the JIM logs. For more details, see below the jump.
Unlock an encrypted APFS boot drive using Disk Utility
In the event that you need to unlock an unbootable boot drive using Apple File System (APFS) encryption, it’s possible to do so using Disk Utility and one of the following authentication credentials:
- The password to a FileVault-enabled account on the drive
- A personal recovery key
For more details, see below the jump.
Recent Comments