Archive
AutoPkg recipes for OS X Lion and OS X Mountain Lion OS installers now available
Now that Apple has made direct download links available for Lion and Mountain Lion, I’ve written AutoPkg .download and .pkg recipes for the following OS X installers:
These recipes will download the disk images linked to the relevant KBase articles, extract the installer packages stored inside the disk images and rename the disk images and installer packages with the OS name and version number.
One thing to be aware of is that the downloaded installers do not themselves install the relevant version of OS X. Instead, they install the Install.app for that version of OS X into the /Applications directory.

Another thing to know is that the downloaded installers are signed using Software Update signing certificates which expired in 2019. As of June 30th, 2021, I do not know if Apple is planning to re-sign the installers with the current Software Update signing certificate.

One of the consequences of this is that I cannot use AutoPkg’s code signature verification as part of the AutoPkg recipes, since AutoPkg’s current code signature verification will error when it hit the expired certificates. If Apple does choose to re-sign these certificate with valid non-expired signing certificates, I’ll add code signature verification to the recipes.
If you do need to use these installers, setting the system clock on your Mac to a date and time before the October 24th 2019 expiration date will allow these certificates to appear as valid again and any expiration-related issues should go away.
The AutoPkg recipes are available via the links below:
OS X Lion: https://github.com/autopkg/rtrouton-recipes/tree/master/OSXLion
OS X Mountain Lion: https://github.com/autopkg/rtrouton-recipes/tree/master/OSXMountainLion
Slides from the “MDM: From “Nice to Have” To Necessity” session at Jamf Nation User Conference 2019
For those who wanted a copy of my MDM talk at Jamf Nation User Conference 2019, here are links to the slides in PDF and Keynote format.
- PDF – https://tinyurl.com/JNUC2019PDF
- Keynote – https://tinyurl.com/JNUC2019Keynote
For those folks at the talk who were interested in Privileges and ProfileCreator, please see the links below:
- Privileges: https://github.com/SAP/macOS-enterprise-privileges
- ProfileCreator: https://github.com/ProfileCreator/ProfileCreator
AutoPkg recipes for macOS Sierra, OS X El Capitan and OS X Yosemite OS installers now available
Now that Apple has made direct download links available for older OS installers, I’ve written AutoPkg .download and .pkg recipes for the following macOS installers:
These recipes will download the disk images linked to the relevant KBase articles, extract the installer packages stored inside the disk images and rename the disk images and installer packages with the OS name and version number.
One thing to be aware of is that the downloaded installers do not themselves install the relevant version of macOS or OS X. Instead, they install the Install.app for that version of macOS or OS X into the /Applications directory.

The AutoPkg recipes are available via the links below:
Apple moving older macOS installers from the Mac App Store
Apple has started making the following macOS installers available outside of the Mac App Store (MAS).
For each listed OS installer, Apple has direct download links via their relevant KBase article for InstallOS.dmg or InstallMacOSX.dmg disk images.


In turn, these disk images contain installers named InstallOS.pkg or InstallMacOSX.pkg.
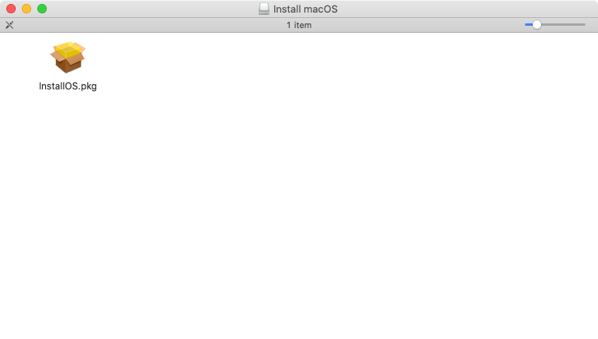

These installers do not themselves install the relevant version of macOS or OS X. Instead, they install the Install.app for that macOS or OS X version into the /Applications directory.




Once the relevant Install macOS or OS X app is available, it can be used to install that OS.
The installers for the following macOS versions are still available via the MAS.
They can also be downloaded on macOS Catalina using the softwareupdate tool.
Enabling automatic macOS software updates for OS X Yosemite through macOS Mojave
A while back, I wrote a post on how to enable automatic OS X updates on OS X Yosemite. The methods used to enable automatic macOS updates changed as of macOS Mojave, so let’s take a look at the changes. For more details, please see below the jump.
Identifying which Active Directory account is logged into Enterprise Connect
As more Mac environments move away from binding Macs to Active Directory and using AD mobile accounts, and towards using local accounts in combination of tools like NoMAD and Apple’s Enterprise Connect, it’s become more challenging to identify which people are logged into which computers. While mobile Active Directory accounts will use the username and password of the person’s AD account, there is no such certainty with local user accounts.
Fortunately, my colleague Joe Chilcote recently let me know that it’s possible to query the logged-in user’s login keychain and get the username of the Active Directory account which is logged into Enterprise Connect. This can be accomplished by running the following command as the logged-in user:
/usr/bin/security find-generic-password -l "Enterprise Connect" $HOME/Library/Keychains/login.keychain | awk -F "=" '/acct/ {print $2}' | tr -d "\""
That should produce output similar to that shown below:
computername:~ username$ /usr/bin/security find-generic-password -l "Enterprise Connect" $HOME/Library/Keychains/login.keychain | awk -F "=" '/acct/ {print $2}' | tr -d "\""
AD_username_here
computername:~ username$
It’s also possible to leverage this technique to update the User and Location section of a particular computer managed by a Jamf Pro server. For more information, see below the jump.
Building VMs on ESXi using esxi_macos_vm_creation.sh
As part of my testing workflow, I’ve been using VMs running on a ESXi server running ESXi 6.5. To help me quickly build those VMs, I have been using a script named esxi_macos_vm_creation.sh for building VMs. This script is forked from Tamas Piros’s auto-create script for standing up Linux VMs on free ESXi:
https://github.com/tpiros/auto-create
My fork of the auto-create script is designed to create and configure virtual machines with Apple operating systems as the guest OS, hosted on a VMware ESXi server running on Apple hardware. The script assumes that the virtual machines are built using copied VMDK disk files, where the VMDK files are generated by AutoDMG and vfuse. For more details, see below the jump.
Expanding partition size in an ESXi-hosted macOS VM
As part of working on a project recently, I ran into an unexpected problem with ESXi-hosted Mac VMs. For these VMs, I was creating VMDK files from AutoDMG-generated disk images, using vfuse to convert the disk image into a VM with ESXi-compatible VMDK disk image files.
My workflow looked like this:
1. Create disk image using AutoDMG.
2. Use vfuse to create VMDK files using a command similar to the one shown below:
sudo vfuse -i /path/to/autodmg_created_disk_image_here --esx

3. Upload the VMDK files to a convenient location on my ESXi server
4. Set up a new VM, using copies of uploaded VMDK files for the VM boot disk.
5. Resize the new VM to the desired size using VMware’s vmkfstools utility.
6. Start up the VM.
After logging in, I ran the following command to enable macOS to recognize and use the unallocated space from the VM resizing:
diskutil resizeVolume / R
Normally, this command is able to do a live re-sizing of the boot partition to use all available unallocated space. However, this time the re-sizing process failed and the following error was displayed:


This file contains bidirectional Unicode text that may be interpreted or compiled differently than what appears below. To review, open the file in an editor that reveals hidden Unicode characters.
Learn more about bidirectional Unicode characters
| computername:~ username$ diskutil resizeVolume / R | |
| Note: Your partition map does not use the entire space of your whole-disk. You should use "diskutil repairDisk" and then repeat this command. | |
| Resizing to full size (fit to fill) | |
| Started partitioning on disk0s2 Macintosh HD | |
| Verifying the disk | |
| Verifying file system | |
| Using live mode | |
| Performing live verification | |
| Checking Journaled HFS Plus volume | |
| Checking extents overflow file | |
| Checking catalog file | |
| Checking multi-linked files | |
| Checking catalog hierarchy | |
| Checking extended attributes file | |
| Checking volume bitmap | |
| Checking volume information | |
| The volume Macintosh HD appears to be OK | |
| File system check exit code is 0 | |
| Resizing | |
| Error: -5341: MediaKit reports partition (map) too small; if you recently grew your whole-disk, you should run whole-disk repair | |
| computername:~ username$ |
How to fix this? For more details, see below the jump.
Creating macOS installer disk images for VMware Fusion and ESXi with create_macos_vm_install_dmg
I’ve had a tool available for a while named create_vmware_osx_install_dmg, but it looks like it has reached the end of the road with macOS 10.12.3. The reason for this is because macOS 10.12.4 has introduced a change that prevents the addition of third-party packages to the OS installer. create_vmware_osx_install_dmg uses the addition of a third-party installer package, so unfortunately this tool cannot be used to generate 10.12.4 or later OS installers.
That said, I still want to be able to create macOS installer disk images for VMware Fusion and ESXi, so I’ve forked create_vmware_osx_install_dmg into a new script named create_macos_vm_install_dmg. create_macos_vm_install_dmg will generate stock OS installer disk images for the following OS versions:
- Mac OS X 10.7.x
- OS X 10.8.x
- OS X 10.9.x
- OS X 10.10.x
- OS X 10.11.x
- OS X 10.12.x
This script does not use a third-party package, so it is able to build a macOS 10.12.4 installer disk image. For more details, see below the jump.
Creating multiline login banners
In a number of Mac environments, there is a need or requirement for a login banner (otherwise known as a lock message). This message appears in the following locations:
- FileVault 2 pre-boot login screen
- OS login window
- Screensaver lock window
Brevity is best, as staying within a maximum of three lines permits the banner text to be displayed consistently in all three locations. Exceeding the three-line limit may result in the text being cut off and not fully displayed.
You can set this banner text from the command line using the following defaults command, which should be run with root privileges:
/usr/bin/defaults write /Library/Preferences/com.apple.loginwindow LoginwindowText "My Login Window Text Goes Here"

Being able to consistently set when lines begin and end can be challenging though, as the defaults command is not able to interpret a newline command natively. However, it is possible to set a multi-line login banner and be able to consistently set when lines begin and end. For more details, see below the jump.
Recent Comments